In this blog, we talk about the V-PKI system, which is the back-end system for issuing digital certificates to vehicles.
In my last blog, we talked about digital certificate and how it is used to guarantee the sender’s authenticity and content integrity, in combination with signature algorithms and public key cryptography. At the end of that discussion, I raised the question of how the receiving end (i.e. Bob) obtains the digital certificate to begin with. In this blog, we talk about the mechanism behind it.
It should be noted that digital certificates are used for many different purposes, including establishing session key to encrypt web traffic (“https” or “TLS”). In fact, V2X communication simply reuses this framework and define a system based on it.
Public key infrastructure (PKI)
In short, Public Key Infrastructure (PKI) is the back-end system that manages digital certificates. The word “manage” involves generation, delivery, distribution, use, revocation, and other related functionalities. It’s conceptually similar to CRUD (Create, Read, Update, Delete) in database operations. It’s sort of a lifecycle management system for digital certificates. As the name implies, PKI is an infrastructure (consisting of hardware, software, procedures/protocols, policies/rules, underlying communication, etc.) that facilitates the use of digital certificates.
A PKI system consists of multiple entities called Certificate Authorities (CAs). They are organized in a hierarchical manner, with the highest one called Root CA (RCA). One level below the RCA is one or more Intermediate CA (ICA), and the next level below is called Issuing CA, which generates certificates to the end entity (certificate users). The figure below shows this hierarchical concept.
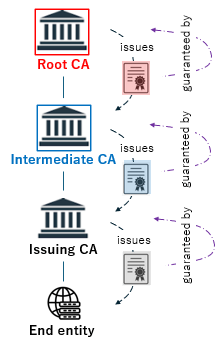
Certificates issued by an entity at one level guarantee the authenticity of the entity one level below. For example, a certificate the RCA (issuer) issues to the ICA guarantees the authenticity of the ICA (certificate holder). Similarly, this chain of guarantee is propagated to the next-level, all the way down to the end entity, which are web servers in the case of websites (TLS/SSL). The trustworthiness of the RCA is known a priori, which is the essential starting point of this PKI concept. This propagating nature of trust bounded by the certificate is called chain of trust. To put it another way, a PKI system is essentially a mechanism that binds the public key in a certificate to its owner.
V-PKI systems
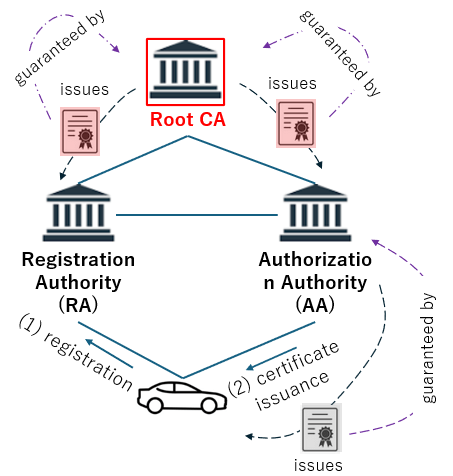
For vehicular communication (V2X), this generic PKI framework is custom-tailored to meet the purpose to issue certificates to vehicles. In this case, intermediate CA is not explicitly defined. There are two entities: Registration Authority (RA) and Authorization Authority (AA). As V-PKI system entities, both RA and AA are issued their own certificates by the RCA to guarantee their authenticity.
Out of RA and AA, the latter is the issuing CA as it is the one that issues certificates to vehicles at the time of registration to the V-PKI system. The RA is responsible for registering end entities (vehicles, in this case) to the V-PKI system, through the registration procedure as defined by the signaling protocol specified by the ETSI ITS standard. As mentioned, the AA actually issues certificates to vehicles after the successful registration with the RA. The following figure is an ETSI-defined V-PKI architecture, which illustrates this relationship.
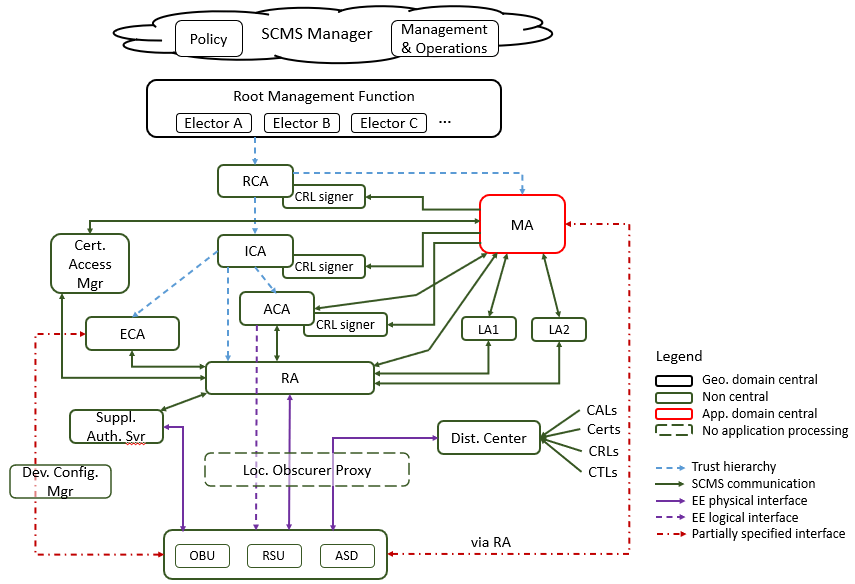
The equivalent V-PKI architecture is defined by IEEE 1609.2. This serves as the base for the ETSI C-ITS architecture. As shown in the figure below, the IEEE 1609.2 architecture defines more system entities with more complex interactions among them. The fundamental idea behind this more complex architecture is to ensure privacy and anonymity of vehicles in such a way that no system entities can identify vehicles (and their owners) by itself without colluding with another entity. This is achieved by splitting up functionalities and limit information visibility/accessibility.
Misbehavior detection and certificate revocation
Aside from issuing certificates to end entities – as a part of managing certificates – another important functionality that the PKI system serves is the revocation of certificates. Certificates are revoked under multiple reasons. In the case of webhost, its certificate can be revoked when the web server is compromised, the website itself is disbanded, the company behind the website goes out of business, or ceases to exist due to a business acquisition, etc.
In case of V-PKI system, certificates issued to vehicles need to be revoked when a vehicle is compromised by an adversary. A compromised vehicle can potentially become the cause of negative consequences to the road safety by transmitting wrong information to mislead other vehicles in the vicinity, etc. In such cases, the affected vehicle needs to be evicted from the communication. It is achieved by revoking the certificates issued to that vehicle.
The receiving entities (vehicles) that are aware of the revocation status of a given vehicle can correctly detect and ignore all messages transmitted by the vehicle that owns the revoked certificates. This way, surrounding vehicles can protect themselves against potentially misleading or wrong information transmitted by this vehicle.
At least this is the theory. However, in reality, it is not so simple. In our next blog, we go a bit deeper about this difficulty.