In this blog, we’re going to talk about the security solution of V2X communication.
In my last post, we talked about the background of the V2X communication and the reason why basic services are broadcast in clear (i.e., sent to any and all recipients within the communication range without encryption). This doesn’t sound like much of a protection — in fact, there’s no protection at all. After all, any device (legitimate or not) capable of receiving messages in that communication channel can receive, store, and analyze them, either in real time or later on. Furthermore, any device that can transmit in that channel can do so, irrespective of whether those entities and messages are legitimate or not.
In other words, basic messages are wide open to eavesdroppers and adversaries who send bogus messages.
This sounds bad from a security point of view. Thus, it requires some sort of assurance, at minimum, that messages are: (1) transmitted by genuine vehicles, and (2) their contents are genuine. With this, receiving entities can at least verify the authenticity of the sender and the integrity of those messages.
The solution to achieve that is to use digital signatures issued by public key infrastructure (PKI). To put it in another way, the only security solution in the basic services in V2X communication is verifying these 2 points only.
Of course, there are service in V2X above and beyond the basic services. These services include such as remote driving, platooning, etc. For these services, either unicast or multicast can be used. In fact, remote driving is probably one of the few use cases in V2X where unicast is used. In those cases, encryption can be applied to guarantee the confidentiality of the communication. Even in those cases, message integrity through the use of digital signature is an important element to the security of V2X communication.
Digital signature
Digital signature ensures that the message is unaltered (i.e. messages are not tampered). It uses public-key cryptography (PKC) such as the elliptic curve digital signature algorithm (ECDSA).
PKC involves the use of two keys, a public key and a private key. They are like two sides of a mirror. When used in encryption, the key used in encryption and decryption is different. The same principle applies to signature generation: the key used to generate a signature and the one to verify it are different. The following figure illustrates this operation.
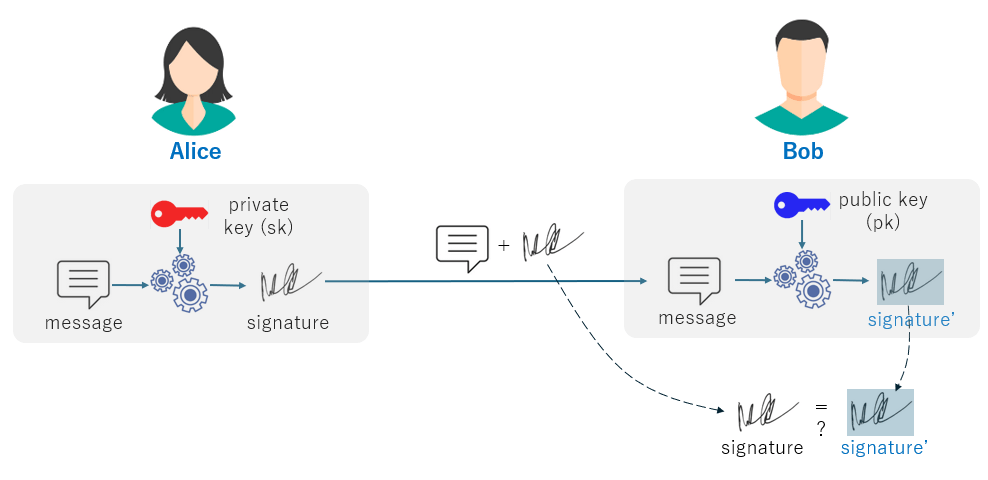
In this figure, Alice sends some message to Bob. After generating a message to send, Alice generates a signature using the message and the private key (often denoted as sk as “secret key”) as the inputs to the signature generation algorithm, such as ECDSA. Alice appends the resulting signature to the message and send them to Bob.
Upon receiving this message (incl. the signature), Bob extracts the message part and, along with the public key, he inputs them to the algorithm. The resulting signature is denoted as signature’. Finally, Bob compares the received signature (attached to the received message) against the calculated signature’. If they match, Bob can assure that the received message is not tampered.
So far so good. But now the question becomes how Bob obtained Alice’s public key to begin with. That’s where PKI comes in, which probably takes a blog by itself. We’ll discuss it in the next blog.